Cybersecurity Awareness Month 2017: Tips to protect yourself from phishing
Phishing is an attempt at identity theft using email and fraudulent websites to obtain personal data, such as account names, passwords, social security numbers, credit card numbers or other personal identification information.
Criminals and/or hackers will send emails to lists of email addresses they have either found or stolen online. These emails can come from spoofed or legitimate email addresses of previously compromised users. The messages themselves can range from being very generic (phishing) to highly customized (this targeted form of phishing is known as spear phishing). The phisher’s goal is to trick the recipient into performing some action, which often involves clicking on a link that leads to a fraudulent website resembling the real website. The fraudulent site typically requests that the victim provide personal information, such as an account name and a password. Once the victim enters this information, nothing may happen. But this “nothing” is far from innocuous. The page may reload or the website may redirect to the real website so that the victim thinks there was a typing or system error. Thus, the victim promptly re-enters the information and re-submits. Because this is now the real site, the log-in is successful, and the victim does not think twice about the original link or the fraudulent site.
Before we get into tips on how to protect yourself, let’s start with learning how to spot a phishing email.
Challenge: Is this email legitimate?  At first glance, this email certainly looks legitimate. The “From” line shows “Vanderbilt Mail Team,” the link appears to direct to a “Vanderbilt E-mail Portal,” and it is signed by the “Email Administrator.”
At first glance, this email certainly looks legitimate. The “From” line shows “Vanderbilt Mail Team,” the link appears to direct to a “Vanderbilt E-mail Portal,” and it is signed by the “Email Administrator.”
Before we label this as a legitimate email, let’s take a closer look using the eight tips below.
Tip 1: Check the embedded links, but don’t click any.
Move your mouse cursor over any links in the body of the email. A little box will pop up, exposing the URL. Ask yourself: “Does the link go to where it claims to, or should, go?”
Tip 2: Verify the display name of the sender.
Move your mouse cursor over the displayed name of the sender (the “From” line). The little box that pops up when you hover your mouse cursor over the sender’s name will be the email address from which the email originated.
Tip 3: Check the body of the message.
Look at the spelling and grammar of the message. Does it appear correct with respect to who typed and sent the message? This can be tricky and subjective. If the email is from a friend, does it look like other emails that friend has sent you in the past regarding grammar, spelling, punctuation and language? On a similar note, if the email claims to be from an authority figure or department, does the grammar, spelling, punctuation and language make sense?
Tip 4: Beware of threatening or urgent language.
Does the body (or subject line) of the message contain an urgent or threatening tone? Language that instills panic or urgency is used quite frequently by criminals because it effectively forces you to act without thinking.
Tip 5: Check the signature of the message.
Does the signature look correct? Is it vague? Does it lack contact details?
Tip 6: Don’t click on or open unexpected attachments.
If you are not expecting an attachment from the sender, do not click on or open any attachment. Check with the sender first to verify that he/she did in fact send you the unexpected attachment. In doing so, use a different communication method to contact the sender, such as a phone call, text, or instant message. If email is the only form of contact you have with the sender, email him/her asking for verification through a phone call.
Tip 7: Don’t believe the graphics.
The email may include a logo that looks legitimate, but this does not make the email legitimate. Anyone can copy/paste a logo or graphic.
Tip 8: Don’t give up personal information.
Vanderbilt University, financial institutions and most legitimate companies will NEVER ask you for personal details though email. They will NEVER ask you for things like social security numbers, passwords, your mother’s maiden name, etc.
Using these eight tips, let’s take a closer look at the email from the challenge: 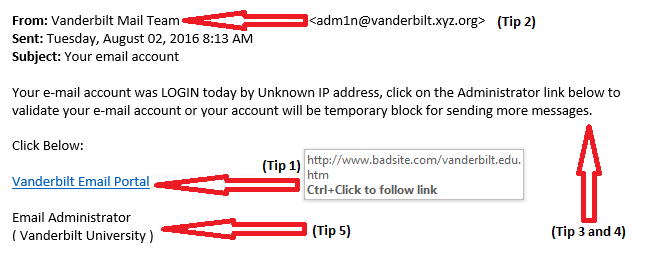
- Hover the mouse over any link within a suspicious email. In doing so, you will realize that clicking will take you to “http://www.badsite.com/Vanderbilt.edu.htm” instead of to a “Vanderbilt Email Portal” as advertised. Take a close look at this URL. First, it is not a Vanderbilt website; the link is part of the domain badsite.com’s website. The “Vanderbilt.edu.htm” portion of the link is merely a webpage within the domain website of badsite.com.
- Hover the mouse cursor over the sender’s display name to reveal the email address (NOTE: This function will only work in an actual email. The above images are .jpg files that do not enable hovering capabilities). The email shown is from “adm1n@vanderbilt.xyz.org” (phishy in itself). Notice that this is not a Vanderbilt domain. If the sender was from Vanderbilt, you could confirm this by seeing an “@vanderbilt.edu” domain address. Keep in mind that criminals usually try to make their fake email addresses look very similar to their targets (@vanderbilt.com, @vandy.edu, @it.vanderbilt.edu, etc.)
- Check the grammar. This email contains clear grammatical, punctuation and spelling errors.
- Check for the use of urgent and threatening language. This email contains both: “Validate your email account or lose access now!”
- Check the email signature. This email’s signature is “Email Administrator,” which is very vague. It contains no real contact details; thus, this should raise a red flag.
With five red flags, we can confidently conclude that this is a phishing email. If you receive an email that raises any flags when you use the above tips, immediately report the suspicious email (instructions below).
REMEMBER: Vanderbilt IT and HR will NEVER ask you to verify an account for ANY reason via email. If you receive an email stating that you need to re-verify your account, please report it to the VUIT Help Desk by calling (615) 343-9999 or by submitting a ticket.
How do I report a suspicious email? Report suspicious to the VUIT Help Desk by calling (615) 343-9999 or by submitting a ticket.
How do I correctly forward a suspicious email, if requested?
In Outlook, when you forward the suspected phishing email, forward it as an attachment. Forwarding the suspicious email as an attachment will preserve email headers, any attached files and other pertinent information. To perform this function in Outlook, select the “home” tab, click on the “respond” section, and select “more” from the dropdown menu. After clicking “more,” select “forward as attachment.”
For additional general information about phishing and how to protect yourself, please contact VUIT Incident Response at phishing@vanderbilt.edu.