VerifyU – Vanderbilt IT’s New Information Security Program
Dec. 20, 2018—(Joe Howell/Vanderbilt) Vanderbilt’s prominence as a preeminent higher education institution with a national footprint makes it a target-rich environment for cyber threats. The university experiences a vast number of attempted attacks daily that target its users, systems and data, and the threats continue to increase in viability. An effective response to combat these evolving threats...
Enroll now in Multi-Factor Authentication
Nov. 14, 2018—Vanderbilt University is taking the next steps in the fight against cyberattacks by deploying a Multi-Factor Authentication (MFA) solution, Duo. MFA is the requirement to provide two different ways of verifying your identity when logging into a secure environment. MFA uses proof of identity through the combination of something you know (e.g., password) and something...
Protect yourself from cybercriminals
Oct. 11, 2018—If you know you are at risk for a wreck when riding a bike then you’ll wear a helmet right? It should be no different when using the Internet and computer technologies.Everyone is at risk for a wreck because attacks against individuals and families are growing. These attacks are increasing, in part due to major...
Cybersecurity Awareness Month 2018: Tips to protect yourself from spear-phishing
Oct. 7, 2018—Be aware! Malicious individuals are using email to pose as Vanderbilt leaders in an attempt to steal our personal information and attack our institution. In recent weeks, we have had many instances of a type of email attack called “spear-phishing” all across Vanderbilt. This tactic is a ramped-up version of “phishing,” which is something most...
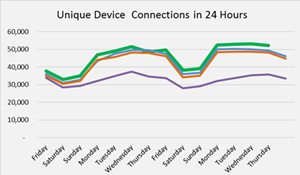
VUIT’s Network Services connects more student devices than ever
Sep. 7, 2018— Even though our student populations stays rather static each year, the number of devices brought to the university increases as does the resources these devices use, such as bandwidth. We typically see an increase of about 3-5% in the number of “things” connecting to the network. This varies from smart phones, laptops, tablets, and...
Network Services provides support for Beyoncé/Jay-Z concert
Sep. 7, 2018—Network Services provided network support for the Beyoncé/Jay-Z concert at Dudley Field on August 23. Over 60 hours of network service support was provided, which included coordination with concert support staff and setting up network access. Network ports and wireless access were provided in parking garages where the singers’ temporary living quarters were setup, in...
VUIT Tech Hub and volunteers assisted over 600 students during move-in weekend
Sep. 7, 2018—Back-to-school initiatives went smoothly and the team has received positive feedback. The Tech Hub welcomed 625 freshmen and their families. Eight of the ten freshmen houses received a walk-through by VUIT staff to address questions and concerns, and students, faculty, and staff utilized the network at an even greater capacity than in 2017.
VUIT Service Delivery prepares classrooms for new school year
Sep. 7, 2018—• 1000+ computer labs, kiosks, and classroom systems were imaged and physically cleaned. • Over 160 systems for faculty, researchers, and staff were added or life-cycled. • 300 systems were moved. • 20+ multi-function devices and printers were new or upgraded. • 293 AV-equipped learning spaces were tested for functionality and any maintenance issues were...
Best Practice Suggestions for Your Online Profile Information
Aug. 8, 2018—Vanderbilt email addresses are readily available on the web and can contribute to attacks like the most recent issue with our Listserv. When online, share your contact information — email addresses, cell phone number, etc.— judiciously, knowing that anything posted on the web is public. VUIT recommends the following best practices: Treat your Vanderbilt email address...
Cybersecurity Awareness Month 2017: Block malware from infecting your computer
Oct. 25, 2017—By definition, malware is malicious software that infects computers, resulting in activity against the interests and/or intentions of the computer’s regular user/owner. The effects of malware could be as benign as slower performance and as malignant as loss of data, attacks on other machines, or worse. Trying to recover from data loss or attacks on...